With presidential primaries battling for news inclusion during the quickly advancing coronavirus pandemic, it feels like we are at a transitional minute for society and business. Open social events are being dropped, schools are changing to online educational programs, numerous individuals went to advanced instruments to keep some similarity to ordinariness. It’s been basic to carefully change our work environments and training to have the option to work successfully. Those organizations ready to utilize innovation well to continue onward and reexamine their plan of action for the future by digital transformation will be ones in front of their opposition.
While today a bigger number of organizations have a work from home workforce, by far most of organizations we see have for the most part conventional work at the workplace setups. While we hope the current coronavirus disturbance is brief, it might be the following pandemic that requires a formalized continuous reaction. Regardless of whether today or “tomorrow,” being “work from home ready” is something that should hop to the top of the need list for CEOs and board chiefs.
Be Ready for “Work from Home”
The capacity to work from home is an advantageous to many employees value, many organizations come up short on the technology infrastructure to offer that capability without some sacrifices to “business as usual”. However, one unexpected outcome of COVID-19 is that organizations understand the advantages of digital transformation.
Enterprise Architecture
Gone are where each worker works out of one brought together solid ERP framework that is secured on the corporate system. Specific applications currently offer upgraded highlights for your industry and plan of action. Associating those applications with the correct innovation interface and standard information models gives better enterprise insights with a lighter technical footprint. Hosting these in the cloud improves versatile access to frameworks and information, with better, quicker and progressively secure associations.
Collaboration Tools
Recall the days when you needed to sign into the organization VPN to get to your business messages? It felt extraordinary to in the long run remotely share project plans, financial models and reports on the file server. Skype and other communicating mediums with our PCs and mobiles. That development hit overdrive in the previous scarcely any years. Vital activity following, cloud document sharing and video conferencing are empowering preferred collaboration over ever previously, requiring no face to face nearness.
Companies Turning to Digital Marketing to Survive COVID-19
Businesses will turn out to be more dependent than any other time in recent memory on their digital strategy. Larger organizations are ending up in the situation of having conceivably lost millions through cancelled events. Discussing little B2B organizations or associations depend on the yearly circuit of public exhibitions and shows to network and assemble client relations. For smaller business particularly, used to getting new clients through verbal referrals or on the quality of a hard-won notoriety, their loss is coming as a stun. Digital is probably going to be the winner here.
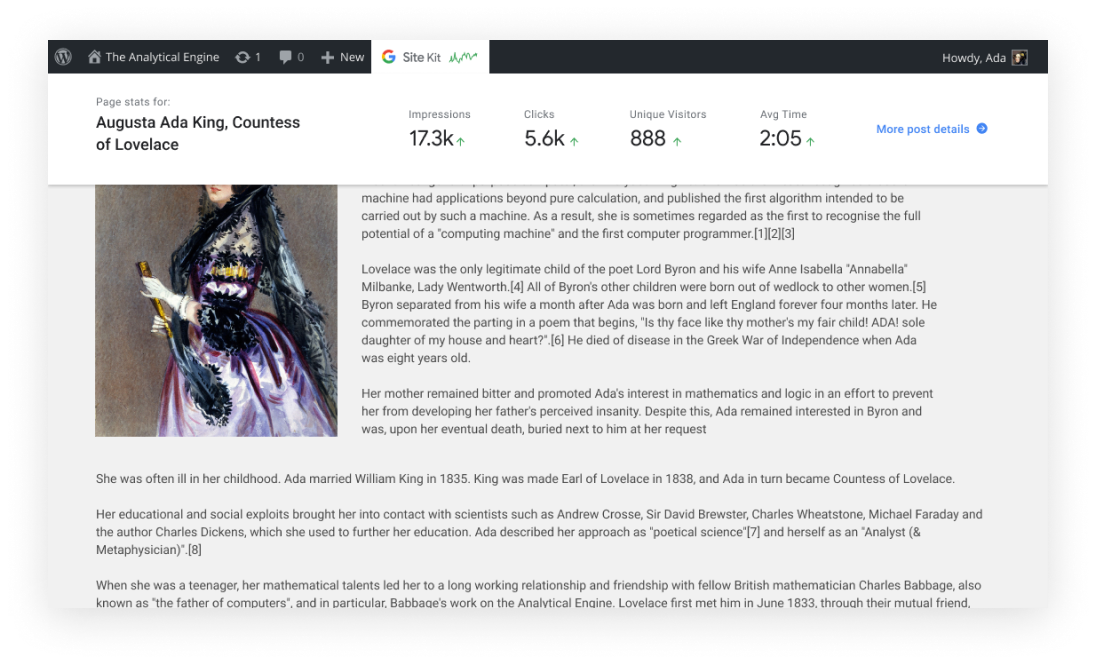
Being bound to the workplace or even the home as opposed to out and about on deals visits or at occasions, implies advertisers have more opportunity to create digital strategies. This implies looking into where your clients can be found online, and how various methodologies and strategies may affect your success. In the event that your association recently put token endeavors into digital channels on the grounds that like a great deal of different organizations, you had constructed your networks offline and that had consistently appeared to work this is the ideal opportunity to return to them. That could be as straightforward as giving your website and social pages a revive, or an increasingly inventive methodology.
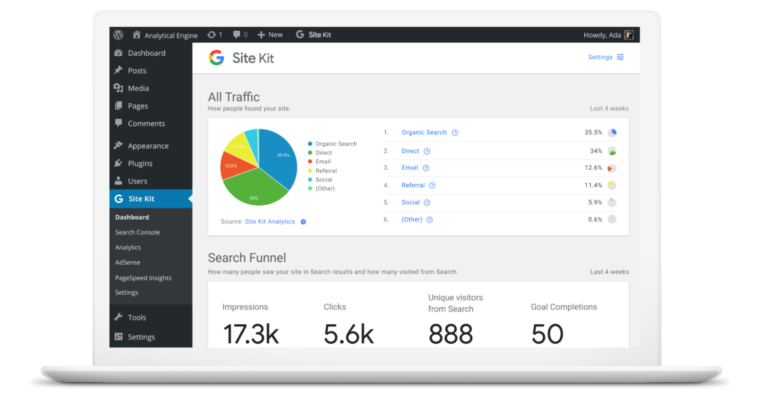
Increase in Social media activity with a jump of 29%
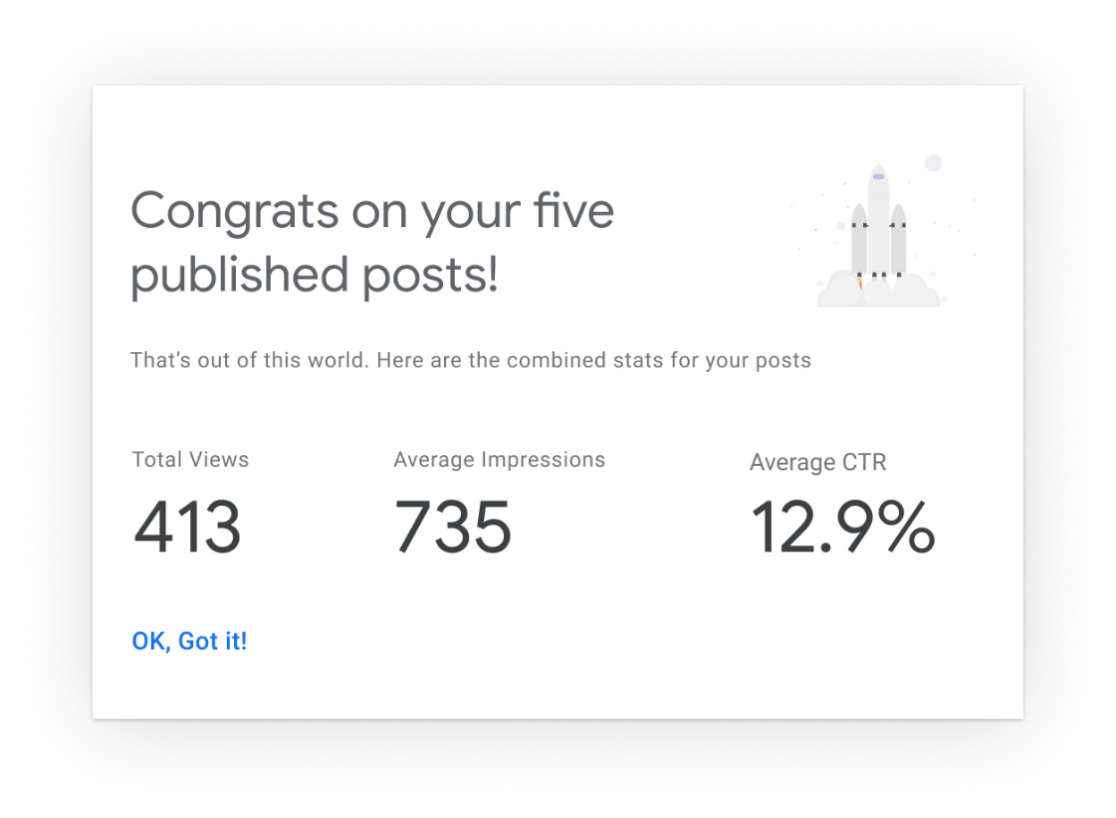
At the point when the main way you can be social is with the help of social media, application introduces for social platforms go up. After a moderate post-Christmas decline, we’ve seen a consistent growth in social media marketing activity throughout the previous a month in a row.
The last time advertising spend for social media was this high was not long before Thanksgiving in November 2019. Anticipate that this category should keep developing particularly applications and platforms that empower live, real-time video interaction.
Why? Introverts may like the shutdown, yet extroverts need their social time.
Taking a glance at the Bigger Picture of Digital Transformation
The COVID-19 pandemic has showcased the value of IT and digital transformation and organizations should use this opportunity to quicken the progress. As organizations develop to turn out to be progressively digital, an ever increasing number of associations with clients will presently happen on a screen than in person. This digital transformation endeavors start with making new records on the web. Digital identity is an overlooked yet truly great individual in an organizations digital transformation strategy because organizations must check that an individual’s digital identity coordinates their physical character when leading business online.
For as long as not many years, digital account opening has been at the highest priority on the rundown of technologies organizations plan to include or replace, yet COVID-19 is pushing digital transformations to the front of the line.